Benefits of Multi Factor Authentication
The benefits of multi factor authentication (MFA) cannot be underestimated. Traditional passwords are not good enough today to keep your data and online accounts secure.
How secure is your connection to this article? I expect you have a good antivirus product installed on your device, which is potentially complimented by a good quality anti-malware solution.
If you are very security conscious, you could even be reading this article over a good quality Virtual Private Network (VPN) solution.
However, if you are not using MFA, when it is available for accessing your accounts, then all other cybersecurity measures can potentially be bypassed.
This article describes what MFA is and introduces you to the concepts that make it easy to understand, and therefore easy to set up and use.
We look under the bonnet at how the MFA process typically works, and then delve into the rationale behind the benefits of multi factor authentication we all experience.
Join The Human Byte — Get The Ultimate BIOS Update Guide
- Receive the Ultimate BIOS Update Pack
- Includes a set of checklists, flowcharts, and your Beep Code Finder support your BIOS update process
- Also includes a full set of eBooks including a Survival Guide and step-by-step Support Guide
- Receive regular emails with practical information you can use
- I only use your e-mail for the newsletter. Unsubscribe anytime.
What is MFA Exactly?
MFA is the process of verifying you are who you say you are, by validating at least two different methods of authentication, each from a different category of factors.
To experience the benefits of multi factor authentication, you need to understand the three basic elements, or factors, that can be used in the MFA process. These are:-
- Something you know (Also known as Knowledge Factors)
- Some you have or own (Also known as Possession Factors)
- Something you are (Also known as Inherence Factors)
 Benefits of Multi Factor Authentication
Benefits of Multi Factor AuthenticationThe Three MFA Elements Example
Source:- doubleoctopus.com
Something you know is generally associated with what is commonly known as Single Factor Authentication (SFA) methods, such as a username, password, PIN (Personal Identification Number), and security questions.
Usernames tend to be an e-mail address or a common work or reference which we tend to remember for most accounts.
Passwords, or Passphrases, can vary in length and complexity. They are the weak link today when used on their own, but can still play a useful role in the MFA process.
To exploit the full benefits of multi factor authentication, employ the common approach for generating more secure passphrases by taking the first letters of a famous song chorus, and amend some letters into UPPERCASE and symbols. For example, take the famous Elvis Presley song, Return to Sender lyrics:-
We Had A Quarrel, A Lover's Spat, I Write I'm Sorry But My Letter Keeps Coming Back
Then your passphrase could be:- Wh@QA!s1w!SbmlKcB
Alternatively, 12 character or more passwords with letters and numbers can be just as difficult to crack.
Pin codes tend to be 4–6 numbers in length, and are either sent to you by text or e-mail as part of an MFA setup, or can be asked upfront on the login page of your online account.
More often than not, you only need to enter a random set of numbers from your PIN when prompted upfront. For example, if your PIN is 293378, you could be prompted for the second, third, and sixth number in the sequence, in which case you would enter numbers 9, 3 and 8.
One-time PINs can also be issued, and if not entered in a certain amount of time, will expire, and another random PIN sequence would need to be issued.
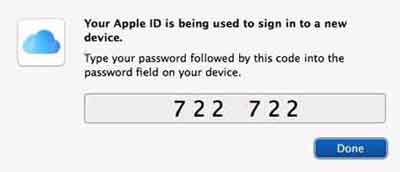 Benefits of Multi Factor Authentication
Benefits of Multi Factor AuthenticationPIN Code Example
Source:- osxdaily.com
Security questions are known as “challenge-response”, and can cover questions such as who is your favourite sports team, to what is your favourite film/movie. These types of questions generally replaced the legacy “what is your mother's maiden name” question.
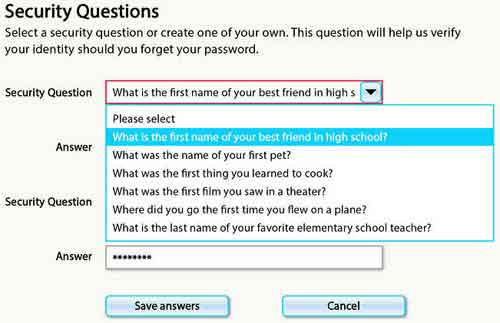 Benefits of Multi Factor Authentication
Benefits of Multi Factor AuthenticationSecurity Question Examples
Source:- wsj.com
Something you have could be a smartphone or other type of mobile device, you have registered the number with the online account provider. This is where the company can send a random code for you to enter in to the login page. It proves you are who you say you are because you have responded from the device you registered.
My bank, for example, will prompt me to enter a random code generated by the banking app on my smartphone before I can log in. I also need to do this when I am authorizing money transactions.
 Benefits of Multi Factor Authentication
Benefits of Multi Factor AuthenticationMy Banking Apps Time Limited Authentication Code Example
'Something you are', is becoming the standard method of authentication and includes methods such as biometric fingerprint scanning, facial recognition, voice or retinal/iris scans.
Smartphones have used inference factors for some time to unlock devices, with fingerprint scanning the preferred standard. High-quality cameras make unique patterns in the iris or on the face easy to detect and use.
Nearly all of my apps, and especially my banking apps, use fingerprint scanning for authentication purposes.
The principle behind the benefits of multi factor authentication is that no safe authentication method exists in isolation. Each element, or factor, has its benefits and drawbacks. The MFA concept is that the benefits of each authentication factor compensates for the weaknesses in each.
Under The bonnet | The MFA Process
The image below shows a typical but complete Multi Factor Authentication process. Assuming your username has been accepted, you are traditionally prompted to enter a password.
This is something you know, and just like the traditional methods of authentication, if you enter your password incorrect more than three times, you run the risk of disabling access to your account.
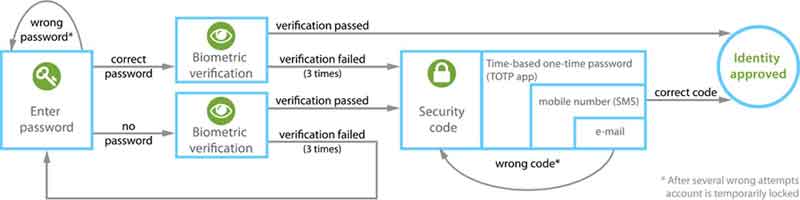 Benefits of Multi Factor Authentication
Benefits of Multi Factor AuthenticationAn Example of the MFA Process
Source:- kb.bioid.com
Occasionally, the provider will not prompt for a password, and will send you straight to the biometric verification phase, or something you are (using something you own to enact). Mobile apps often send you straight to fingerprint verification and don't bother with a password at this stage.
If you successfully negotiate the biometric verification, you are given immediate access to your account. This is known as two-factor authentication, or 2FA.
However, if you fail the biometric verification stage under 2FA circumstances, companies will typically prompt you for the password you entered when you set your account up. Hopefully, you have a note somewhere safe, as this password will rarely be used.
If you successfully entered your password before failing the biometric verification, companies will typically send a random, time sensitive verification code to your registered device, in the form of a text message or e-mail.
Enter this correctly and authentication will be granted. This is something you own, and collectively is known as multi factor authentication.
Why Use MFA?
Passwords are the original and most popular 'security' measure for accessing all types of accounts, whether they be e-mail, social media, entertainment etc.
However, passwords are also the most vulnerable measure to cracking, which is a method used by cyber criminals to work out what your password is, by using a technique called a brute-force attack.
A brute-force attack is a technique for guessing what your password or passphrase is by repeatedly submitting, or guessing, what it is until the correct one is found.
The stronger your password strength is, the more difficult it is to determine through a brute-force attack. A password's strength is usually focused on its length and complexity, i.e. the amount of capital letters, numbers, and symbols used.
However, passwords and passphrases, to a lesser extent, if constructed properly, are still vulnerable. Once they are cracked, they will allow anyone to access your accounts, and then do whatever you can do once inside.
The traditional approach of changing your password to something else if it is cracked, or if the company hosting your account has been subject to a cybersecurity attack, is insufficient today.
Cybercrime is a lucrative business, and simply repeating traditional security measurers of changing your password to something else, that can be cracked, simply cannot continue.
In addition, trying to remember all of your password becomes a headache as the number of accounts you need increases. This leads to people using the same password or passphrase for all accounts.
If the cyber criminals successfully crack your password for one account, they could have access to all of your accounts, and that's a scary thought!
You can buy products that include secure Password Manager Services. These can help secure your passwords and will even auto-enter your login details, so you don't have to remember them.
However, companies are adopting multi factor authentication to compliment your password, or in some cases, replace it completely.
The main benefits to us as users of MFA include improved security. The MFA principle in inherently more secure than the traditional password.
Cybercriminals need to have all three elements, i.e. something you know, something you have, and something you are, before they can get into your accounts.
MFA also simplifies logins to multiple accounts. This is achieved using Single Sign On (SSO) methods. Once you authenticate using MFA, a company such as Google can use SSO to automatically log in to other apps or accounts provided by that company, across multiple devices.
If you are logging in from a known location or device, a one-time passcode can be sent by text, for example, and would not be needed every time you require access.
The contextual behaviour elements of SSO enables companies to profile your login behaviour, including geo-locations and the devices being used to authenticate to their online accounts and applications.
If there is a compromise, for example, an attempt to access your account from another country, the company can lock all your account(s) as a security measure, or inform you to change an element of your authentication process.
In addition, MFA includes various countermeasures to combat evolving password theft techniques. Cybersecurity criminals are constantly improving their techniques for 'guessing' your password, including:-
- Key logging — Recording your keystrokes or taps on a touchscreen device;
- Phishing — Fraudulent attempts to elicit your authentication details by spoofing legitimate looking e-mails from your bank or other online account provides;
- Pharming — Method of redirecting you to a spoof website that looks like a legitimate website.
There are also various benefits to organizations, including regulatory compliance.
Benefits of Multi Factor Authentication | Final Thoughts
The benefits of multi factor authentication are clear. It is an excellent method of security authentication to all apps and online accounts. If it is available, use it.
However, it is also critical to create passwords that are difficult to crack. Have a look at the eComputerZ Strong Random Password Generator Tool to help you set the right complexity and uniqueness for all of your passwords.
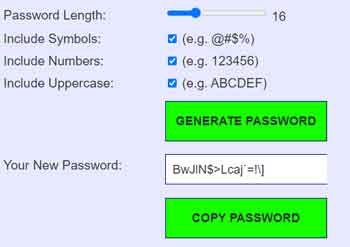 Benefits of Multi Factor Authentication
Benefits of Multi Factor AuthenticationStrong Random Password Generator Tool
You may find different providers implement MFA slightly differently. However, an understanding of the three basic elements of MFA, which is something you know; something you own, and something you are, will make whatever combination companies implement, in whatever order, clearer and easier to understand and navigate.
To learn more about the benefits of multi factor authentication, take a look at the following MFA articles, and watch the short video below.
